Security Solutions - Claroty
Why ICS/OT security is necessary

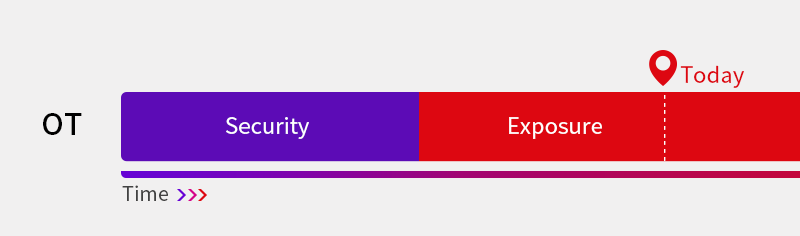
OT security today
- Legacy ICS/OT infrastructure that had not considered security/resilience from the initial design stage (e.g. difficulty with security patches)
-
An environment of gradual convergence
between IT and OT (e.g. supply chain integration for productivity) -
Critical infrastructure with warnings
of constant security threats (e.g. possible occurrence of national disaster)

Claroty Platform overvie
Providing ICS/OT environment security to improve visibility and resilience + full multispectral solutions for risks in operation

 Continuous Threat Detection (CTD)
Continuous Threat Detection (CTD) 
 Secure Remote Access (SRA)
Secure Remote Access (SRA)
-
Identify
- Discover/detect detailed and intuitive ICS/OT asset data up to the serial I/O level
- Perceive ICS/OT infrastructure risks and analyze integrated event correlation
- Interpret/test and automatically analyze the connections among OT operation elements and all communications
-
Detect
- Detect security threats and vulnerabilities
- Detect application of the latest patch and installed applications/files
- Continuously monitor abnormal actions and symptoms in the security/operation of the OT environment
- Subdivide the logical virtual network of OT network
-
Protect
- Detect changes in firmware, setpoint, and command in ICS/OT infrastructure
- Control/manage remote and site access, record videos of remote jobs
- Manage the process for remote access requests and jobs
-
Respond
- Provide threat intelligence for ICS/OT infrastructure and index safety/risk
- Prioritize measures for ICS/OT security/operation threats
Perfect OT security solution
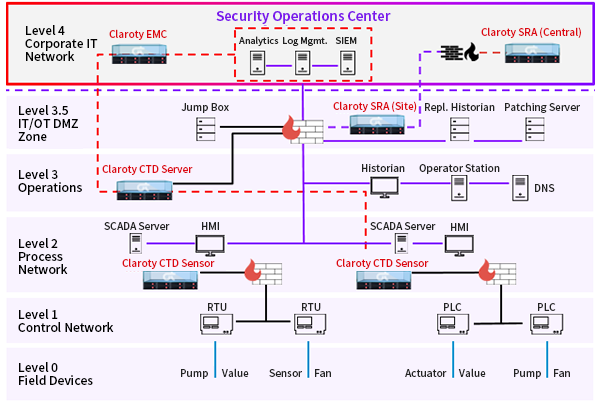
The Claroty Platform is comprised of Continuous Threat Detection (CTD), Enterprise Management Console (EMC), and Secure Remote Access (SRA) systems. This solution does not require agent installation and can be integrated smoothly with the existing IT security infrastructure. It also provides the most extensive OT security functions in the industry in terms of visibility, threat detection, vulnerability management, threat classification and reduction.
-
Continuous Threat Detection (CTD)
- Provide overall OT visibility by perceiving and managing all assets automatically
- Detect known threats and zero-day threats on a real-time basis
- Constantly monitor the vulnerability of each asset
- Provide OT network microsegments
-
Secure Remote Access (SRA)
- Protect, control, simplify OT remote access
- Minimize risks caused by remote access users
- Support best practices of IT/OT security
- Constantly inspect maintenance and compliance with regulations
-
Enterprise Management Console (EMC)
- Quickly and safely distribute without the risk of shutdowns
- Provide integrated IT-OT management designed for SOC
- Provide integrated support for warning and risk analysis for the site overall
- Smoothly integrate with the IT security infrastructure
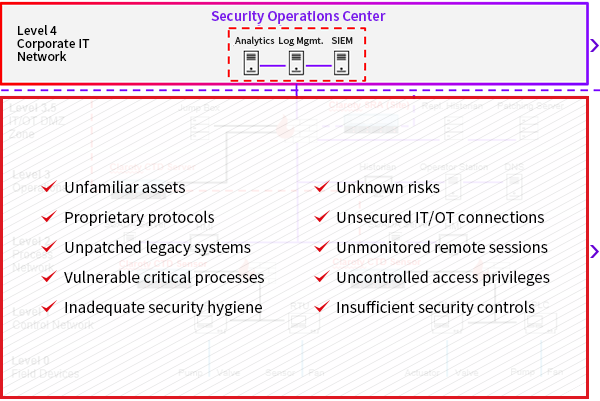
OT threat detection
By using five analysis engines, CTD automatically profiles all assets, communications and processes
in the OT network for the real-time detection of abnormal symptoms, known threats, and zero-day threats.


- Claroty threat analysis engines

-
OT visibility
The Claroty Platform implements total OT visibility as follows using an
excellent protocol support range and asset recognition method.- Asset visibility includes all devices on the OT network (e.g. series network) and the extensive attributes of each device (e.g. model number, firmware version).
- Network visibility includes all network sessions and bandwidths, performed tasks, changes, and other related information.
- Process visibility tracks the code sections, tags, and all OT actions for all processes that include OT assets.
-
OT vulnerability management
Visibility provided by the Claroty Platform is expanded by detecting security vulnerabilities and threats in the OT network. The key functions are as follows.
- Total CVE: Real-time search and assessment of total CVE in the network asset
- Attack vector: Automatically providing potential OT threat scenarios
- Risk dashboard: Customized dashboard providing a risk analysis overview
-
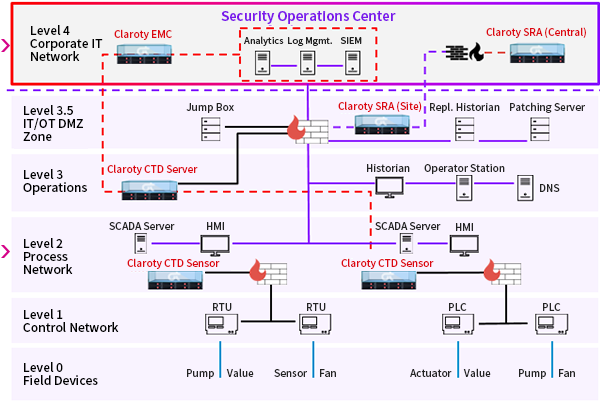
Typical Enterprise Network
-
Enterprise Network with Claroty Platform Deployed
Applicable industries


Cases of Claroty Platform establishment/operation by global companies to monitor OT asset security visibility and ICS symptoms
-
ABInBev (No. 1 global beer manufacturer) 380 Sites, 7 Regions,
SOC Enablement -
CocaCola(No. 1 global soft drink manufacturer) 100 Sites,
Multiple Bottlers -
BHP (Biggest global mining company) 50+ Sites, 3 Regions,
SOC enablement -
CLP(Major power generator in Asia) 65 Sites, 3 Regions,
SOC Enablement -
Pfizer(No. 1 global pharmaceutical company) 65 Sites,
Global Rollout -
Schneider Electric(Major ICS manufacturer) 200 Sites, 3 Regions,
SOC Enablement
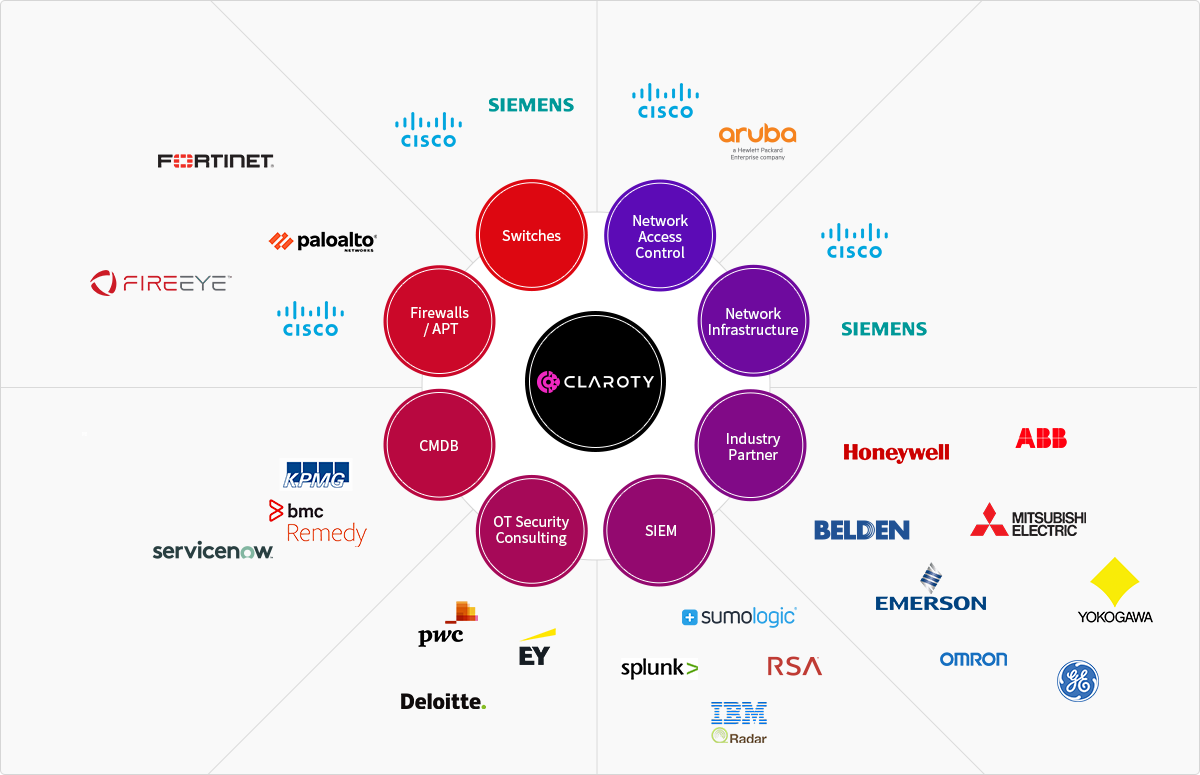
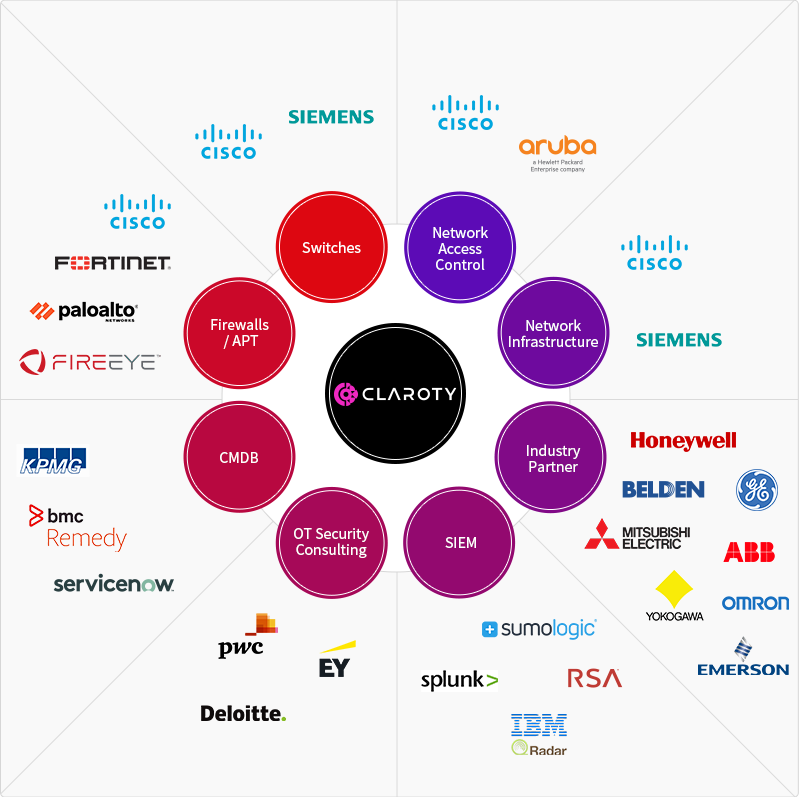
Security solution link and technical partner ecosystem